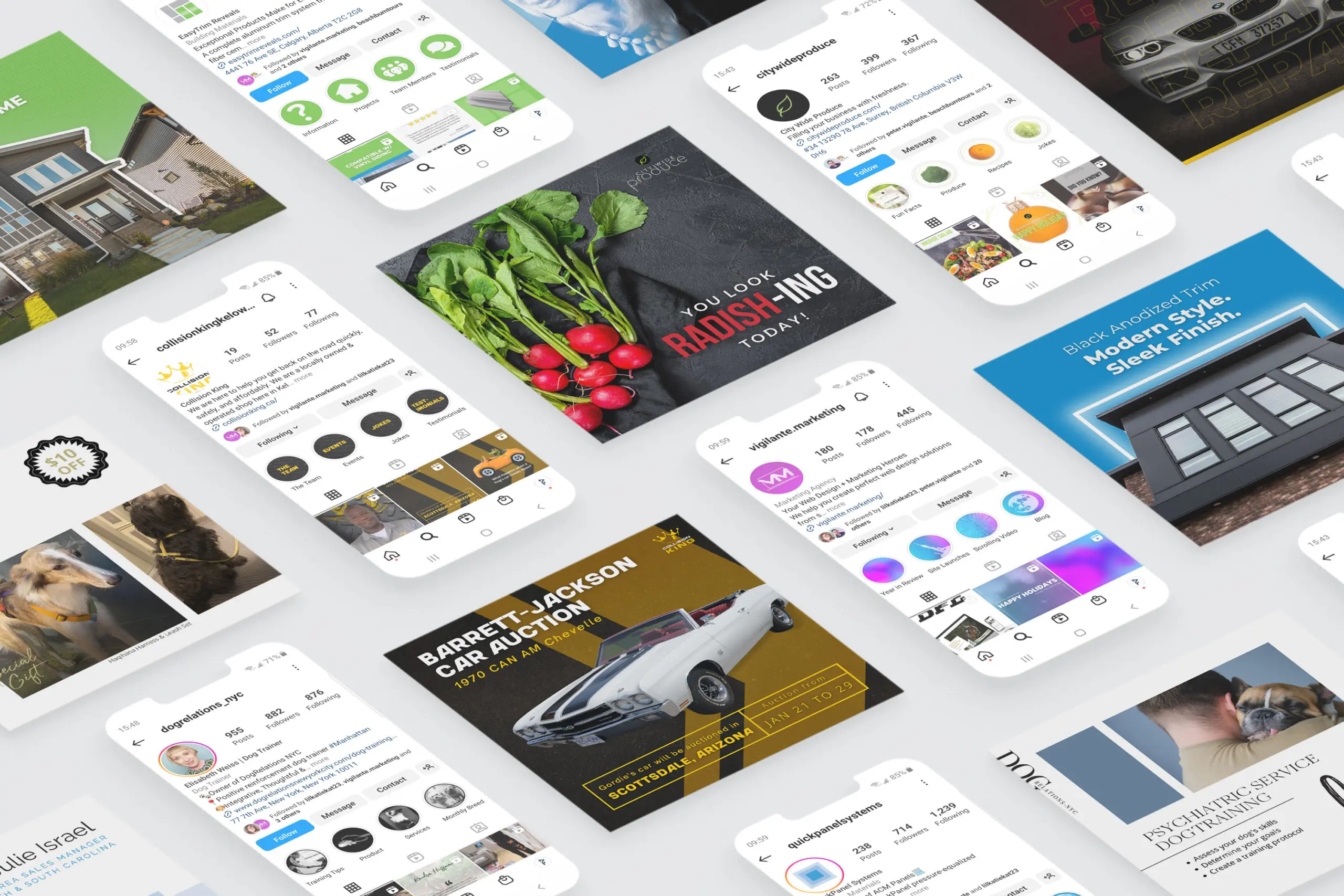
Peter and his team are the real deal! They not only created amazing websites for our business, but have helped us with Facebook and Google ads, attracting our ideal clients and increasing our revenue. We have been in business for 10 years, have gone through multiple web developers/marketing teams, and we finally found our team in Vigilante Marketing!
Let us help you discover what your business’s goals are, who your target clientele is, and how you want your business to be visually represented.